You may find yourself in a situation where you’ve gained some juicy hashes from a previous attack, but you’re unable to crack these hashes into clear-text. Well no worries, you can still look into passing the hash. Prerequisites: Hash obtained from previous attack. See any one of these posts for Continue Reading
AD Hacking: NTLM Relay Tutorial
A good URL with slides about NTLM relay can be found here. I recommend giving it a quick read and maybe watching a video to understand what is happening. Prerequisites: Domain controller with Active Directory setup. See this series, to set up your lab environment. Kali Linux Two (2) Windows Continue Reading
AD Hacking: Getting Meterpreter Session
Getting a Meterpreter session is always a wonderful thing. You can elevate privileges, dump hashes, clear windows logs, download/upload files, and more. Prerequisites: Domain controller with Active Directory setup. See this series, to set up your lab environment. Kali Linux Windows 10 VM, joined to a domain Setting your environment Continue Reading
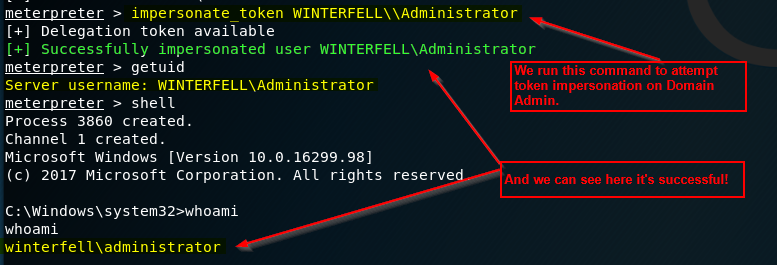
AD Hacking: Token Impersonation Tutorial
Here we will perform a token impersonation. There are a few ways an adversary can access tokens of elevated accounts, such as a domain administrator. For this walk-through, we will simply use Meterpreter. Prerequisites: Domain controller with Active Directory setup. See this series, to set up your lab environment. Kali Continue Reading
Obligatory Post-OSCP Post
I have finally earned my OSCP certification, and I figured I’d update the ol’ blog with a couple thoughts of what I really think helped me out mentally. This post will not serve as a guide for specific tools, techniques, or tactics — rather to explain my mindset through out Continue Reading
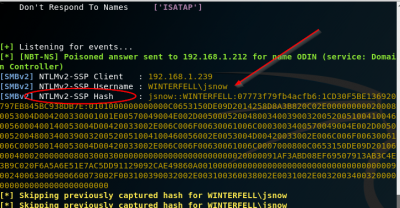
LLMNR Poisoning – Part IV: Attacking
Part I: Part I: Requirements / Installing Operating SystemsPart II: Part II: Setting up Active DirectoryPart III: Part III: Joining Windows 10 to Domain, Mapping Shared Folder, & Quick Kali ConfigurationPart IV: Part IV: Attacking This is it! The final post of the series. We will not conduct our attack Continue Reading
LLMNR Poisoning – Part III: Joining Windows 10 to Domain, Mapping Shared Folder, & Quick Kali Configuration
Part I: Part I: Requirements / Installing Operating SystemsPart II: Part II: Setting up Active DirectoryPart III: Part III: Joining Windows 10 to Domain, Mapping Shared Folder, & Quick Kali ConfigurationPart IV: Part IV: Attacking Now that we’ve created a domain, a domain user, and a share, we’re going to Continue Reading
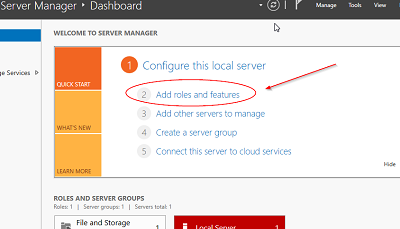
LLMNR Poisoning – Part II: Setting up Active Directory
Part I: Part I: Requirements / Installing Operating SystemsPart II: Part II: Setting up Active DirectoryPart III: Part III: Joining Windows 10 to Domain, Mapping Shared Folder, & Quick Kali ConfigurationPart IV: Part IV: Attacking Welcome back to LLMNR Poisoning. This is Part II of the series of posts providing Continue Reading
LLMNR Poisoning – Part I: Requirements / Installing Operating Systems
Part I: Part I: Requirements / Installing Operating SystemsPart II: Part II: Setting up Active DirectoryPart III: Part III: Joining Windows 10 to Domain, Mapping Shared Folder, & Quick Kali ConfigurationPart IV: Part IV: Attacking Introduction: This is part one of a series of posts I’ll be making on performing Continue Reading