A while back I was assigned a mobile application penetration test. I was met with a unique challenge of testing an Android application, but found there to be challenges with Android accepting user supplied certificates (i.e. burp suite cert). Because of this, I couldn’t properly proxy the traffic from my Continue Reading
Tutorial
Your IPv6 is Showing [CarolinaCon]
IPv6 is often seen as a mystical protocol by many folks and its scary to think about making the transition from IPv4. What’s even scarier is it’s likely already in place within your organization and attackers can leverage it against you! Further, companies are quickly rolling out IPv6 within their Continue Reading
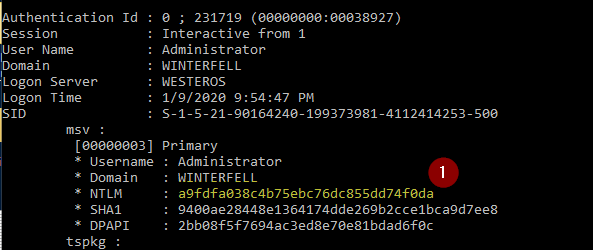
AD Hacking: Mimikatz Part I
Hello all, this is going to be a two part series on Mimikatz and its powerful uses. First and foremost, if you haven’t set up an active directory lab environment yet, please do so by visiting this link –> https://mattschmidt.net/2019/05/10/llmnr-poisoning-part-i-requirements-installing-operating-systems/ and follow Part I and II of that series. Note: Continue Reading
AD Hacking: Pass The Hash
You may find yourself in a situation where you’ve gained some juicy hashes from a previous attack, but you’re unable to crack these hashes into clear-text. Well no worries, you can still look into passing the hash. Prerequisites: Hash obtained from previous attack. See any one of these posts for Continue Reading
AD Hacking: NTLM Relay Tutorial
A good URL with slides about NTLM relay can be found here. I recommend giving it a quick read and maybe watching a video to understand what is happening. Prerequisites: Domain controller with Active Directory setup. See this series, to set up your lab environment. Kali Linux Two (2) Windows Continue Reading
AD Hacking: Getting Meterpreter Session
Getting a Meterpreter session is always a wonderful thing. You can elevate privileges, dump hashes, clear windows logs, download/upload files, and more. Prerequisites: Domain controller with Active Directory setup. See this series, to set up your lab environment. Kali Linux Windows 10 VM, joined to a domain Setting your environment Continue Reading
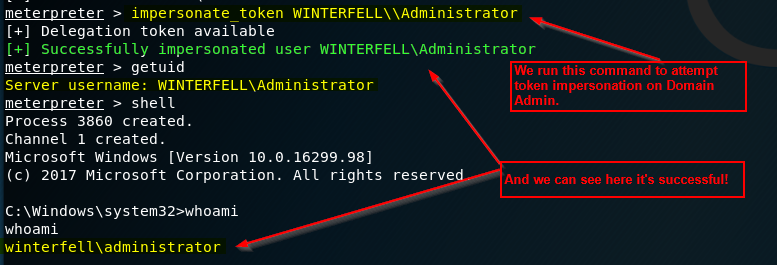
AD Hacking: Token Impersonation Tutorial
Here we will perform a token impersonation. There are a few ways an adversary can access tokens of elevated accounts, such as a domain administrator. For this walk-through, we will simply use Meterpreter. Prerequisites: Domain controller with Active Directory setup. See this series, to set up your lab environment. Kali Continue Reading
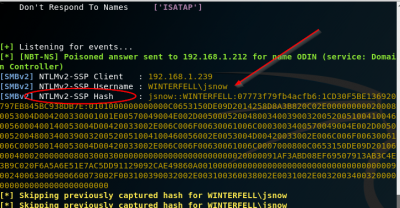
LLMNR Poisoning – Part IV: Attacking
Part I: Part I: Requirements / Installing Operating SystemsPart II: Part II: Setting up Active DirectoryPart III: Part III: Joining Windows 10 to Domain, Mapping Shared Folder, & Quick Kali ConfigurationPart IV: Part IV: Attacking This is it! The final post of the series. We will not conduct our attack Continue Reading
LLMNR Poisoning – Part III: Joining Windows 10 to Domain, Mapping Shared Folder, & Quick Kali Configuration
Part I: Part I: Requirements / Installing Operating SystemsPart II: Part II: Setting up Active DirectoryPart III: Part III: Joining Windows 10 to Domain, Mapping Shared Folder, & Quick Kali ConfigurationPart IV: Part IV: Attacking Now that we’ve created a domain, a domain user, and a share, we’re going to Continue Reading
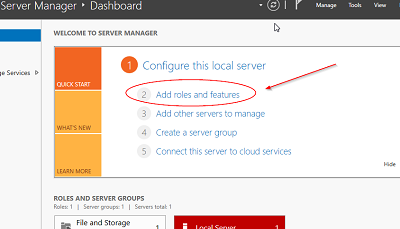
LLMNR Poisoning – Part II: Setting up Active Directory
Part I: Part I: Requirements / Installing Operating SystemsPart II: Part II: Setting up Active DirectoryPart III: Part III: Joining Windows 10 to Domain, Mapping Shared Folder, & Quick Kali ConfigurationPart IV: Part IV: Attacking Welcome back to LLMNR Poisoning. This is Part II of the series of posts providing Continue Reading

![Your IPv6 is Showing [CarolinaCon]](https://mattschmidt.net/wp-content/uploads/2021/04/mitm6.png)